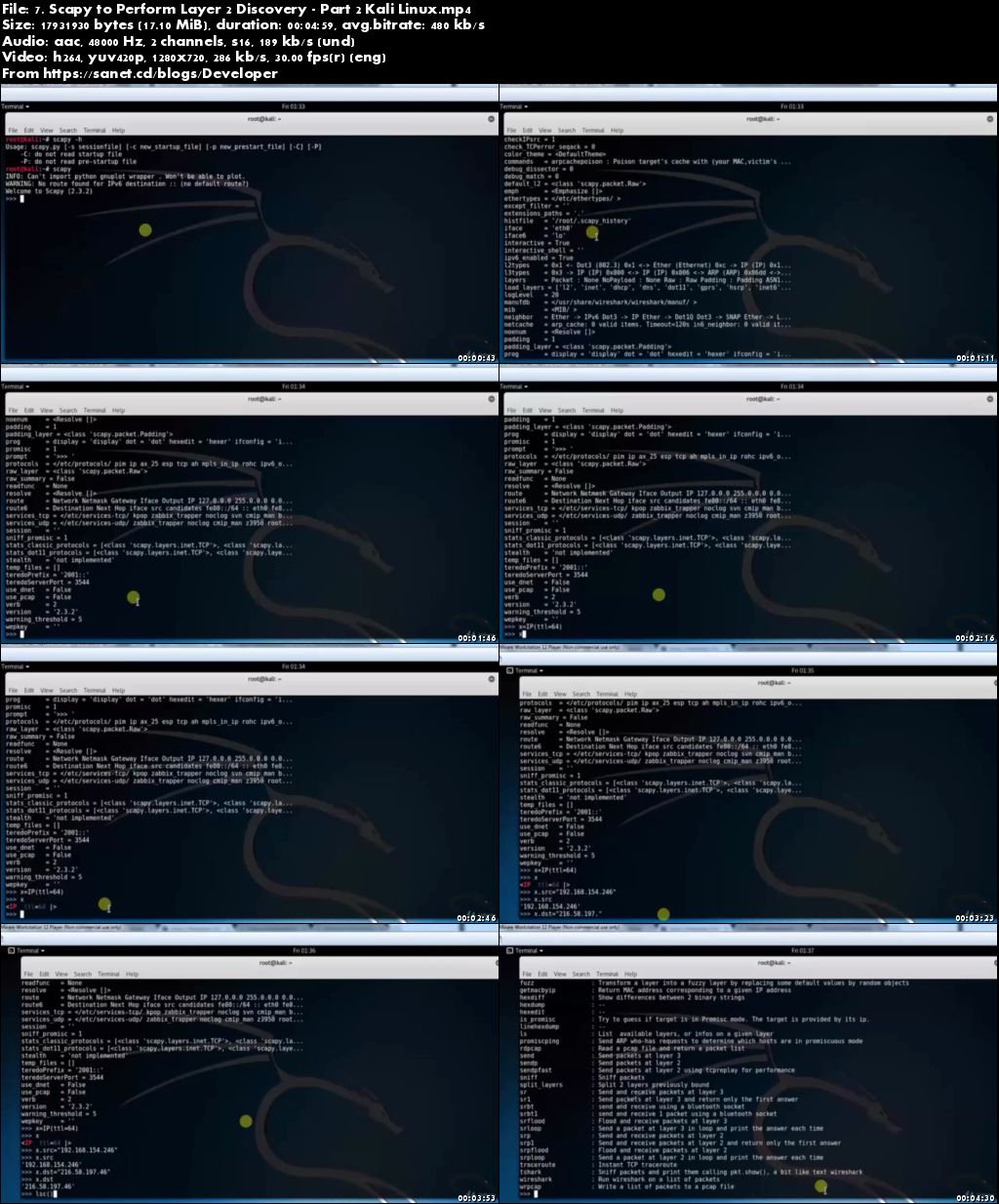
Genre: eLearning | Language: English
This video tutorial will help you to learn different types of most advanced Ethical Hacking tools
What Will I Learn?
Perform basic to advanced tasks in Kali Linux
Configure services and turn your Kali Linux into a server
Complete ethical hacking tasks from Kali Linux
Network hacking and Security
Wifi hacking and Security
Dos and Ddos attacks
Understand how Linux commands can be used by hackers
Requirements
Laptop
Internet connection
Description
This is 100% practical based course , with Intellectual theory. You’ll learn the most advanced Ethical Hacking tools.
“Kali Linux” is one of the best open-source security packages of an ethical hacker, containing a set of tools divided by categories.
Kali Linux is a Debian-derived Linux distribution designed for digital forensics and penetration testing.
Installing Kali Linux is a practical as it provides more options to work with combine tools.
This course gives a complete understanding on Kali Linux and explains how to use it in defense Security.
It is maintained and funded by Offensive Security Ltd.
All of the resources to build the labs are free.
It will definitely be a plus if you are familiar with the basic concepts of any Linux operating system.
Kali contains several hundreds of tools which are geared towards various information security tasks, such as Penetration Testing, Security research, Computer Forensics and Reverse Engineering.
What skills will you gain?
Perform basic to advanced tasks in Kali Linux
Configure services and turn your Kali Linux into a server
Complete ethical hacking tasks from Kali Linux
Network hacking and Security
Wifi hacking and Security
Dos and Ddos attacks
Understand how Linux commands can be used by hackers
Many more
Features of kali Linux:
More than 600 penetration testing tools included
Open source Git tree
Wide-ranging wireless device support
Custom kernel, patched for injection
Developed in a secure environment
GPG signed packages and repositories
Multi-language support
Completely customisable
Advantages of Kali Linux:
Single user, root access by design
Network services disabled by default
A minimal and trusted set of repositories
Who is the target audience?
IT Engineers
Ethical hackers
Hobbyist
Network Administrators and Operators
Security policy makers
Pentesters
Download rapidgator
https://rg.to/file/c2e7b40fafce50d870a813cd589f72b8/udm_CompleteHackingToolsKaliLinux.part1.rar.html
https://rg.to/file/09eda9e188f69efa29c8de18c6c67649/udm_CompleteHackingToolsKaliLinux.part2.rar.html
https://rg.to/file/fdcae19fff591502b9c1082f08e66404/udm_CompleteHackingToolsKaliLinux.part3.rar.html
https://rg.to/file/3dc51e931390ff86d6254a7171c36c08/udm_CompleteHackingToolsKaliLinux.part4.rar.html
Download nitroflare
http://nitroflare.com/view/3ABE733F6D110E7/udm_CompleteHackingToolsKaliLinux.part1.rar
http://nitroflare.com/view/AAB95CBBD30D67A/udm_CompleteHackingToolsKaliLinux.part2.rar
http://nitroflare.com/view/CD7AD268B897DB0/udm_CompleteHackingToolsKaliLinux.part3.rar
http://nitroflare.com/view/859FDC1A7E1B9C0/udm_CompleteHackingToolsKaliLinux.part4.rar
Download 百度云
你是VIP 1个月(1 month)赞助会员,
