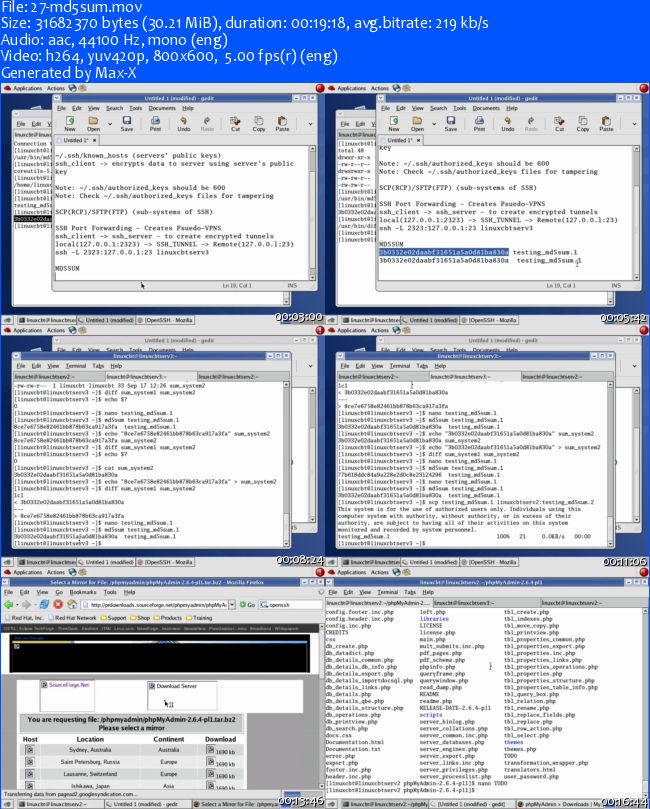
LinuxCBT Basic Security Edition
English | .MOV | h264, yuv420p, 800×600, 5.00 fps(r) | aac, 44100 Hz, mono | 1.24 GB
Genre: E-learning
Boot Security
Explore Dell PowerEdge BIOS Security-related features
Discuss concepts & improve Dell PowerEdge BIOS security
Explain run-time boot loader vulnerabilities
Explore single-user mode (rootshell) and its inherent problems
Modify default GRUB startup options & examine results
Secure boot loader using MD5 hash
Identify key startup-related configuration files & define boot security measures
Identify key boot-related utilities
Confirm expected hardware configuration
Discuss INIT process, runlevel configuration & concepts
Explore & tighten the security of the INIT configuration
Shell Security
Confirm expected applications
Discuss Teletype Terminals (TTYs) and Pseudo Terminals (PTS)
Identify common TTYs and PTSs
Track current TTYs and PTSs – character devices
Discuss concepts related to privileged and non-privileged use
Restrict privileged login
Use SSH and discuss TTYs
Discuss the importance of consistent system-wide banners & messages
Define and configure system banners for pre and post-system-access
Identify user-logon history and correlate to TTYs
Identify current user-connections – console-based and network-based
Use lsof to identify open files and sockets
Syslog Security
Discuss Syslog concepts and applications
Explain Syslog semantics – facilities & levels – message handling & routing
Focus on security-related Syslog facilities
Examine security logs managed by Syslog
Configure Network Time Protocol (NTP) on interesting hosts
Secure NTP configuration
Ensure time consistency to preserve log-integrity
Configure Syslog replication to preserve log-integrity
Identify log discrepancies between Syslog hosts
Reconnaissance & Vulnerability Assessment Tools
Discuss Stage-1 host/network attack concepts
Upgrade NMAP reconnaissance tool to increase effectiveness
Identify NMAP files
Discuss TCP handshake procedure
Discuss half-open/SYN connections
Perform connect and SYN-based host/network reconnaissance
Identify potential vulnerabilities on interesting hosts derived from reconnaissance
Examine NMAP logging capabilities
Perform port sweeps to identify common vulnerabilities across exposed systems
Secure exposed daemons/services
Perform follow-up audit to ensure security policy compliance
Discuss vulnerability scanner capabilities and applications
Prepare system for Nessus vulnerability scanner installation – identify/install dependencies
Generate self-signed SSL/TLS certificates for secure client/server communications
Activate Nessus subscription, server and client components
Explore vulnerability scanner interface and features
Perform network-based reconnaissance attack to determine vulnerabilities
Examine results of the reconnaissance attack and archive results
Secure exposed vulnerabilities
XINETD – TCPWrappers – Chattr – Lsattr – TCPDump – Clear Text Daemons
Install Telnet Daemon
Install Very Secure FTP Daemon (VSFTPD)
Explore XINETD configuration and explain directives
Configure XINETD to restrict communications at layer-3 and layer-4
Restrict access to XINETD-protected daemons/services based on time range
Examine XINETD logging via Syslog
Discuss TCPWrappers security concepts & applications
Enhance Telnetd security with TCPWrappers
Confirm XINETD & TCPWrappers security
Discuss chattr applications & usage
Identify & flag key files as immutable to deter modifcation
Confirm extended attributes (XATTRs)
Discuss TCPDump applications & usage
Configure TCPDump to intercept Telnet & FTP – clear-text traffic
Use Ethereal to examine & reconstruct captured clear-text traffic
Secure Shell (SSH) & MD5SUM Applications
Use Ethereal to examine SSH streams
Generate RSA/DSA PKI usage keys
Configure Public Key Infrastructure (PKI) based authentication
Secure PKI authentication files
Use SCP to transfer files securely in non-interactive mode
Use SFTP to transfer files securely in interactive mode
Configure SSH to support a pseudo-VPN using SSH-Tunnelling
Discuss MD5SUM concepts and applications
Compare & contrast modified files using MD5SUM
Use MD5SUM to verify the integrity of downloaded files
GNU Privacy Guard (GPG) – Pretty Good Privacy (PGP) Compatible – PKI
Discuss GPG concepts & applications – symmetric/asymmetric encryption
Generate asymmetric RSA/DSA GPG/PGP usage keys – for multiple users
Create a local web of trust
Perform encrypts/decrypts and test data-exchanges
Sign encrypted content and verify signatures @ recipient
Import & export public keys for usage
Use GPG/PGP with Mutt Mail User Agent (MUA)
AIDE File Integrity Implementation
Discuss file-integrity checker concepts & applications
Identify online repository & download AIDE
Install AIDE on interesting hosts
Configure AIDE to protect key files & directories
Alter file system objects and confirm modifications using AIDE
Audit the file system using AIDE
Rootkits
Discuss rootkits concepts & applications
Describe privilege elevation techniques
Obtain & install T0rnkit – rootkit
Identify system changes due to the rootkit
Implement T0rnkit with AIDE to identify compromised system objects
Implement T0rnkit with chkrootkit to identify rootkits
T0rnkit – rootkit – cleanup
Implement N-DU rootkit
Evaluate system changes
Bastille Linux – OS-Hardening
Discuss Bastille Linux system hardening capabilities
Obtain Bastille Linux & perform a system assessment
Install Bastille Linux
Evaluate hardened system components
NPING – Flexible Packet Crafting
Discuss benefits
Download and install
Explore typical usage
Nikto – Web Server Vulnerability Scanner
Download and install
Discuss configuration options
Scan web servers
Evaluate results
http://rg.to/file/d001229dc3a1f7ebef273a6d11a21da3/Basic_Security_Edition.part1.rar.html
http://rg.to/file/f9a8eff09a937a851af97496aeed0506/Basic_Security_Edition.part2.rar.html
http://rg.to/file/48c6f1aa299c3ef1aca0edd61482532d/Basic_Security_Edition.part3.rar.html
http://rg.to/file/f645b2f444778c4095c9c81ce47abfca/Basic_Security_Edition.part4.rar.html
http://rg.to/file/85820dd93c5fcd9a2fb1a542c26c7429/Basic_Security_Edition.part5.rar.html
http://rg.to/file/75e37199430bef65c2df45668a7809d6/Basic_Security_Edition.part6.rar.html
http://uploaded.net/file/jp8wwxri/Basic_Security_Edition.part1.rar
http://uploaded.net/file/uhbgeftc/Basic_Security_Edition.part2.rar
http://uploaded.net/file/89gbn26y/Basic_Security_Edition.part3.rar
http://uploaded.net/file/0gr9omxi/Basic_Security_Edition.part4.rar
http://uploaded.net/file/xc2l5cu1/Basic_Security_Edition.part5.rar
http://uploaded.net/file/wek23gzu/Basic_Security_Edition.part6.rar
你是VIP 1个月(1 month)赞助会员,
转载请注明:0daytown » LinuxCBT Basic Security Edition
与本文相关的文章
- Automation Testing Strategies with ASP.NET Core
- Master Next.js for Beginners 2024 with projects
- JavaScript 10 Projects in 10 Days Course for Beginners 2024
- Mastering Nextjs 14, From Beginner to Advanced Form Creation
- Linux and Bash: Going Pro
- React and NodeJS Websockets: A Rapid Guide
- Bioinformatics Data Analysis Crash Course Python R and Linux
- Quick Jump Into Lightning Web Components!
- Mastering Frontend Development: HTML to Project Deployment
- Blazor Deep Dive – From Beginner to Advanced in .NET 8
- Master Next.js 14: Build a Powerful Expense Tracker App
- Next-Gen Web Development: JavaScript & AI Essentials